In today’s digital landscape, cybersecurity is more crucial than ever. With cyber threats lurking around every corner, businesses and individuals must fortify their defenses. One effective way to identify vulnerabilities is through Cybersecurity Pen Testing. But what exactly does this entail?
Imagine having a team of ethical hackers probing your systems to uncover weaknesses before the bad actors do.
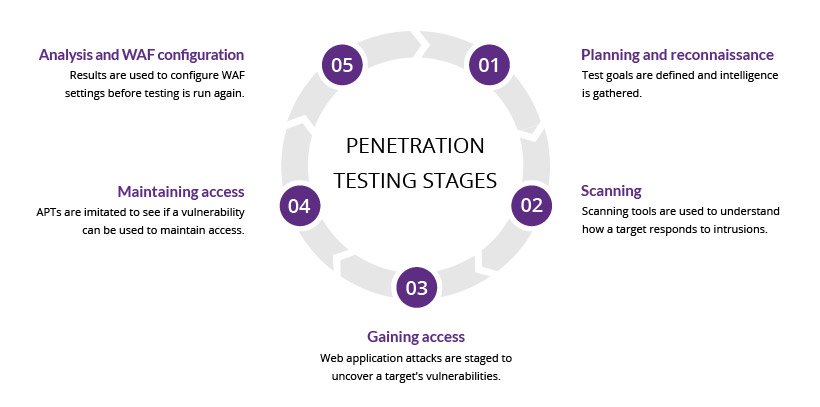
Cybersecurity Pen Testing, or penetration testing, is a proactive approach to identifying vulnerabilities in systems. It simulates cyberattacks to evaluate an organization’s security posture. By attempting to exploit weaknesses, testers can reveal potential entry points for hackers.
Organizations engage in Pen Testing to safeguard sensitive data and maintain compliance with industry regulations. This process helps build robust defenses against real-world threats while providing valuable insights into how well existing security measures perform under pressure. Embracing Cybersecurity Pen Testing allows companies to stay one step ahead of malicious actors in today’s digital landscape.

Cybersecurity Pen Testing plays a crucial role in safeguarding digital assets. It identifies vulnerabilities before malicious actors can exploit them. By simulating real-world attacks, organizations gain valuable insights into their security posture.
This proactive approach not only strengthens defenses but also builds trust with clients and stakeholders. Regular pen tests ensure compliance with industry regulations, reducing the risk of costly breaches. Investing in cybersecurity pen testing is investing in business continuity and reputation management. Embracing this practice ultimately leads to a more secure digital environment for everyone involved.
Typically conducted by ethical hackers, pen tests analyze how effective your current defenses are. They map out potential entry points for attackers while providing insight into areas that need improvement. By understanding these basics, organizations can better prepare themselves against real-world threats in the ever-evolving landscape of cybersecurity.
About Telecom VoIP
Telecom Service Corporation was founded in October 1990 in the state of New York. TSC Initially operated as a “Telecommunications Interconnect” company — selling, installing and maintaining telecommunications equipment and services.
Early in our history, we supported financial trading organizations, utilizing trading turrets systems as their main form of voice communications. TSC bought and sold trading turret equipment on the secondary market, offering it at 50% savings over buying new equipment. TSC dealt with most of the major brokerage houses on Wall Street including Cantor Fitzgerald, Morgan Stanley, CIBC, Bank of Montreal, Bank of Scotland, and JP Morgan Chase.
With the advent and perfection of Voice over Internet Protocol (VoIP), Telecom Service Corporation refocused our business away from premised based PBX’s hardware to the more cost effective and resilient Cloud based systems that promote connectivity and mobility redundancy.
Rebranded as TSC VoIP, our company continues to operate in the New York City Metropolitan area, currently servicing small to medium size business in the region and throughout the United States.
Get a free quote
TSC VoIP is pleased to offer no-cost, no-obligation quotes for business class phone systems and service. Please provide your contact information below , and one of our knowlegeable experts will contact you to get your quote done right away.